Apple iPhone Hacking Kit Used By Spies, Crypto Scams Could Have US Intelligence Origins

n brief
- Google has identified a sophisticated iOS exploit kit called Coruna containing 23 exploits.
- The toolkit was used by suspected Russian spies and Chinese crypto scammers.
- Security firm iVerify says clues in the code suggest it may have originated from a U.S. intelligence contractor.
Google’s Threat Intelligence Group (GTIG) has uncovered a powerful iPhone hacking toolkit capable of infecting devices when a user visits a malicious website, meaning malware can be transferred without anything being clicked on by the target.
The framework, dubbed “Coruna,” includes five full iOS exploit chains and 23 vulnerabilities targeting iPhones running iOS 13 through 17.2.1. Researchers said some of the exploits rely on previously unseen techniques to bypass Apple’s security protections.
https://platform.twitter.com/embed/Tweet.html?dnt=false&embedId=twitter-widget-0&features=eyJ0ZndfdGltZWxpbmVfbGlzdCI6eyJidWNrZXQiOltdLCJ2ZXJzaW9uIjpudWxsfSwidGZ3X2ZvbGxvd2VyX2NvdW50X3N1bnNldCI6eyJidWNrZXQiOnRydWUsInZlcnNpb24iOm51bGx9LCJ0ZndfdHdlZXRfZWRpdF9iYWNrZW5kIjp7ImJ1Y2tldCI6Im9uIiwidmVyc2lvbiI6bnVsbH0sInRmd19yZWZzcmNfc2Vzc2lvbiI6eyJidWNrZXQiOiJvbiIsInZlcnNpb24iOm51bGx9LCJ0ZndfZm9zbnJfc29mdF9pbnRlcnZlbnRpb25zX2VuYWJsZWQiOnsiYnVja2V0Ijoib24iLCJ2ZXJzaW9uIjpudWxsfSwidGZ3X21peGVkX21lZGlhXzE1ODk3Ijp7ImJ1Y2tldCI6InRyZWF0bWVudCIsInZlcnNpb24iOm51bGx9LCJ0ZndfZXhwZXJpbWVudHNfY29va2llX2V4cGlyYXRpb24iOnsiYnVja2V0IjoxMjA5NjAwLCJ2ZXJzaW9uIjpudWxsfSwidGZ3X3Nob3dfYmlyZHdhdGNoX3Bpdm90c19lbmFibGVkIjp7ImJ1Y2tldCI6Im9uIiwidmVyc2lvbiI6bnVsbH0sInRmd19kdXBsaWNhdGVfc2NyaWJlc190b19zZXR0aW5ncyI6eyJidWNrZXQiOiJvbiIsInZlcnNpb24iOm51bGx9LCJ0ZndfdXNlX3Byb2ZpbGVfaW1hZ2Vfc2hhcGVfZW5hYmxlZCI6eyJidWNrZXQiOiJvbiIsInZlcnNpb24iOm51bGx9LCJ0ZndfdmlkZW9faGxzX2R5bmFtaWNfbWFuaWZlc3RzXzE1MDgyIjp7ImJ1Y2tldCI6InRydWVfYml0cmF0ZSIsInZlcnNpb24iOm51bGx9LCJ0ZndfbGVnYWN5X3RpbWVsaW5lX3N1bnNldCI6eyJidWNrZXQiOnRydWUsInZlcnNpb24iOm51bGx9LCJ0ZndfdHdlZXRfZWRpdF9mcm9udGVuZCI6eyJidWNrZXQiOiJvbiIsInZlcnNpb24iOm51bGx9fQ%3D%3D&frame=false&hideCard=false&hideThread=false&id=2028938464784269632&lang=en&origin=https%3A%2F%2Fdecrypt.co%2F359927%2Fapple-iphone-hacking-kit-used-by-spies-crypto-scams-could-have-us-intelligence-origins&sessionId=8041529d08cf33086e9aad56d213fb53e9a2cdfa&siteScreenName=decryptmedia&theme=light&widgetsVersion=2615f7e52b7e0%3A1702314776716&width=550px
GTIG first identified parts of the toolkit in early 2025 in an exploit chain used by a customer of an unnamed commercial surveillance vendor. The code used a JavaScript framework that fingerprinted devices to determine the iPhone model and operating system version before delivering a tailored exploit.
The same framework later appeared on compromised Ukrainian websites in mid‑2025. Google attributed that campaign to UNC6353, a suspected Russian espionage group, which used hidden iframes to selectively target visiting iPhone users.
ETH
+3.46%$2,146.03
24H7D1M1YMAX
Later in the year, researchers discovered the toolkit again on hundreds of Chinese‑language websites tied to cryptocurrency and finance scams. Those sites attempted to lure victims to visit using iOS devices before injecting the exploit kit.
The report said vulnerabilities used by Coruna have since been patched in newer versions of Apple’s mobile operating system and urged users to update their devices. The exploit kit does not work against the latest versions of iOS.

Google Warns of AI-Powered North Korean Malware Campaign Targeting Crypto, DeFi
Google’s security team at Mandiant has warned that North Korean hackers are incorporating artificial intelligence–generated deepfakes into fake video meetings as part of increasingly sophisticated attacks against crypto companies, according to a report released Monday. Mandiant said it recently investigated an intrusion at a fintech company that it attributes to UNC1069, or “CryptoCore”, a threat actor linked with high confidence to North Korea. The attack used a compromised Telegram account, a…
4 min read
Callan QuinnFeb 10, 2026
Possible U.S. origins
While GITG’s report does not identify the original surveillance vendor customer or who may have developed the kit, researchers for mobile security firm iVerify researchers said elements of the code suggest possible U.S. origins.
“It’s highly sophisticated, took millions of dollars to develop, and it bears the hallmarks of other modules that have been publicly attributed to the U.S. government,” iVerify co-founder Rocky Cole told WIRED. He added that it was the first example uncovered by the firm of “very likely U.S. government tools” being adopted by adversaries and cybercriminal groups after “spinning out of control.”
iVerify estimated roughly 42,000 devices in just one campaign were compromised after analyzing traffic to command‑and‑control servers linked to Chinese‑language scam websites distributing the exploits.
Related Articles

KOFIA Chairman Demands South Korea Join Global Financial Trend
In a significant development for Asian financial markets, Korea Financial Investment Association (KOFIA) Chairman Hwang Seong-hyeop has publicly called for South Korea to introduce...
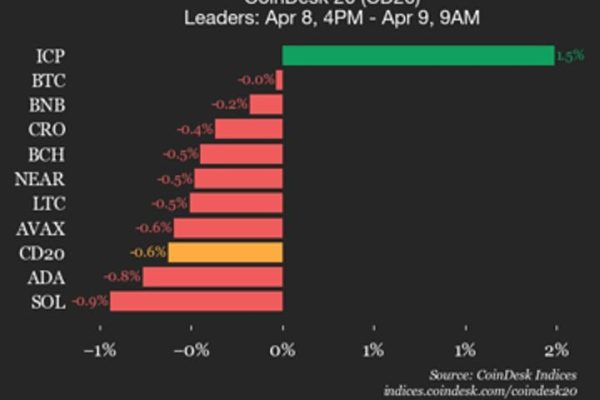
Bitcoin (BTC) trades flat as index declines
CoinDesk Indices presents its daily market update, highlighting the performance of leaders and laggards in the CoinDesk 20 Index. The CoinDesk 20 is currently...

Avalanche – How tired buyers, active sellers are affecting AVAX’s weak rally
Avalanche [$AVAX] rallied by 13.71% in just under 18 hours on Tuesday, 7 April. The move from $8.46 to $9.62 came alongside heavy spot...

SOL may drop below $80 amid ETF outflows and bearish derivatives data
The cryptocurrency market has switched bearish over the past 24 hours following the excellent start to the week. Solana’s $SOL has extended its correction...
